Emerging in mid-2023, ThreeAM is a relatively new but notable ransomware strain that has attracted attention due to its unique use of the Rust programming language and its targeted, manual deployment techniques.
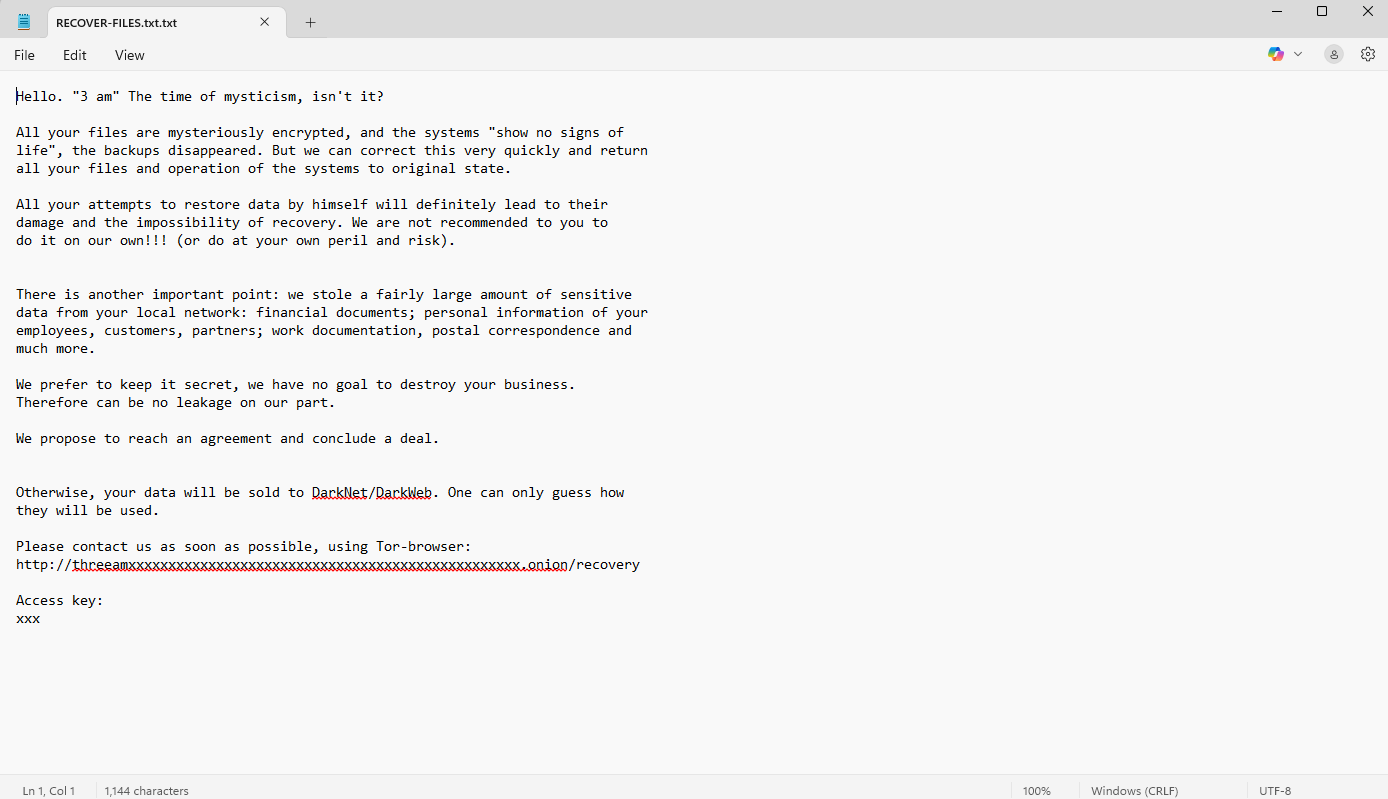
An infection with ThreeAM results in the encryption of systems and critical files, with victims receiving a ransom note, as shown here, demanding cryptocurrency payment in exchange for decryption keys.
If you discover a physical break-in at your offices, your first instinct would be to call the police and touch nothing - understanding the need for a forensic investigation. A cyber-attack requires the same approach.
Your digital environment is a CRIME SCENE. It is crucial to leave the environment untouched to allow for a forensic investigation.
This is not a task for your IT team or MSP. Digital Forensic specialists available 24/7 to assist you, just like in a physical crime.

ThreeAM (also stylised as 3AM) is a rare and emerging ransomware variant first identified in 2023. Unlike many mainstream ransomware operations, ThreeAM appears to be deployed as a backup payload - typically when primary ransomware (such as LockBit) is detected and blocked. This suggests it may be used by affiliates or operators looking to guarantee damage even when initial access fails.
ThreeAM is written in Rust, a modern programming language that offers increased speed and stealth, and can be compiled for multiple operating systems. This makes it more difficult for traditional security tools to detect and analyse.
The group behind ThreeAM uses a hands-on approach, manually deploying the ransomware after gaining remote access through techniques such as phishing, RDP compromise, or exploiting unpatched vulnerabilities. Once inside the network, they attempt to exfiltrate sensitive data before launching encryption, following a typical double extortion model.
ThreeAM is deployed manually, often during late-night hours (hence the name), once attackers have already obtained administrative access to the target environment. The ransomware encrypts files with the .threeamtime extension and leaves behind a note that outlines payment demands and threatens data exposure. ThreeAM has also been observed trying to terminate various security and backup services before launching encryption.
Due to its limited use in the wild, ThreeAM is believed to be operated by a smaller group or as a tool within a larger affiliate network.
ThreeAM was first observed in mid-2023 and has so far been linked to 64 attacks. It appears to be used selectively, often when more established ransomware like LockBit fails due to defensive measures.
Because of this secondary role and its hands-on deployment, it is not as widespread as other strains. However, its stealthy nature and manual attack patterns mean it poses a significant threat, particularly to organisations without strong detection and response capabilities.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
“Global ransomware payments in 2023 topped $1 billion”

Solace Cyber was established in 2021, specialising in Cyber breaches, particularly Digital Forensics and Incident Response, Ransomware, Risk Management, and Information Security, along with Managed Security Services. The leadership team collectively possess over 20 years of experience in the IT and security industry. Solace Cyber is accredited to ISO 27001.
s
%+
A forensic analysis needs to be meticulous and a clean restore and recovery requires a wealth of experience not normally available in an in-house team who must provide a broader range of IT support skills:


Solace Cyber was established precisely for this scenario. We have a well-defined process for handling cyber-attacks like ThreeAM, which involves a 6-step approach:
It includes a thorough digital forensic analysis from step 2 where the output becomes a central component of business recovery. This is because understanding the attack is of critical importance:
It is critical that the analysis of digital evidence is carried out to an agreed plan. This will have been designed to provide the best and earliest chance of discovering a root cause, which is essential to inform remediation/eradication and recovery as well as supporting a legal take-down case if this is applicable. A legal take-down means we can assist in the legal enforcement that stops the criminals from publishing the data, thus undermining the ransom notice.
Solace’s Digital Forensic and Incident Response teams maintain consistent communication throughout. Dedicated Incident Managers and technical engineering leads provide updates during the Cyber Incident Response journey, utilising risk registers and working within change management processes, all from triage through to post-incident, delivering successful business recovery.
Solace Cyber's assistance extends beyond the recovery phase. Following the restoration of your business operations, we collaborate with you to enhance your cyber security posture using a threat-informed methodology. This involves leveraging our Cyber 6 Step Process, designed to comprehensively address cyber threats and vulnerabilities.
Yes, ThreeAM is a form of ransomware. It encrypts data and demands payment for decryption keys, often threatening to leak exfiltrated data unless a ransom is paid.
The ThreeAM ransomware entered your system by one of several ways:
We recommend you adopt policies to:
After recovering from a ThreeAM ransom attack, Solace Cyber recommends that you update your business continuity plan to account for lessons learnt during this attack & recovery.
Most ransomware breaches cost approximately £500K, while smaller email data breaches typically cost around £50K. There is a critical balance between preserving the environment for forensic analysis and quickly recovering it to minimise business interruption. The costs increase the longer it takes to identify and resolve the breach.
A cyber security insurance claim is complex, covering reasonable expenses for investigating and remediating an incident, along with legal fees, business interruption, criminal liability, employment liability, and ransom payments. Although the insurance industry is responsible for facilitating business recovery, cyber insurance is viewed as volatile, and many policies are not being validated correctly.
Finding your way through demands expertise, and that's where Solace Cyber can offer assistance.
Facing genuine pressure, there's a crucial decision to make - one that could rescue your organisation from weeks of operational standstill, reputation damage, and client data loss. Yet, the probability of a favourable outcome remains slim, emphasising the importance of engaging a specialised ransomware incident response team. They are your most viable recourse for navigating a ransomware incident.
The NCSC have documented the deliberations for paying ransomware: https://www.ncsc.gov.uk/ransomware/home
Important Reminder: It is a criminal offense to pay money to people who are subject to financial sanctions. The list of who is subject to financial sanctions is constantly changing.
The latest iteration can be found here: https://www.gov.uk/government/publications/financial-sanctions-consolidated-list-of-targets
Yes. There's a possibility that some of the lost data falls under the category of "Personal Data" belonging to your customers. It's your legal responsibility to safeguard this data, even if it has been lost. Additionally, you may need to notify the Information Commissioner's Office at https://ico.org.uk/.
Your insurer or legal counsel will provide guidance on the necessary steps and how to move forward in this situation.
Solace has experience collaborating with insurers and legal professionals and can offer support in managing this relationship during this challenging period.
A ransomware attack presents the most significant threat to your business by:
In the event of a business interruption, determining your position in the supply chain for any item and sustaining operations become challenges. If the disruption persists, maintaining business continuity becomes paramount. Moreover, upon restoration of systems and data, addressing any backlog of work and establishing operational protocols for the future becomes essential.
Ransomware ranks only behind receivership in terms of its capacity to incapacitate a business.
Action Fraud is the UK’s national reporting centre for fraud and cybercrime. Whether you have been scammed, defrauded, or experienced cybercrime in England, Wales, or Northern Ireland, Action Fraud offers a central point of contact for information on fraud and financially motivated cybercrime.
In the event of a ThreeAM ransom attack on your systems, REMAIN CALM.
DO NOT INTERACT WITH THEM, ATTEMPT TO RESTORE, OR OVERWRITE ANY DATA (explanation above).
Reach out to Solace Cyber at 01202 308818 or complete our form for a callback from one of our specialists.
We'll respond promptly to minimise your business's downtime.

Solace Cyber helps companies across the UK recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 14028838

Solace Cyber
Twin Sails House,
W Quay Rd,
Poole, BH15 1JF
United Kingdom