Underground ransomware is a newer threat that operates primarily through dark web forums and private affiliate networks.
An infection with Underground results in your systems being locked and your data encrypted. Victims are then presented with a ransom demand, often in cryptocurrency, to restore access and prevent stolen data from being published online.
A break-in at your offices would compel you to call the police immediately and touch nothing until they arrive, understanding the need for forensic work to take place.
A cyber-attack requires the same action. Your first responsibility would be to call in the forensic experts and ensure the environment remains untouched.
This is not a job for your IT team or MSP. There are Digital Forensic specialists available 24/7 who can assist you.
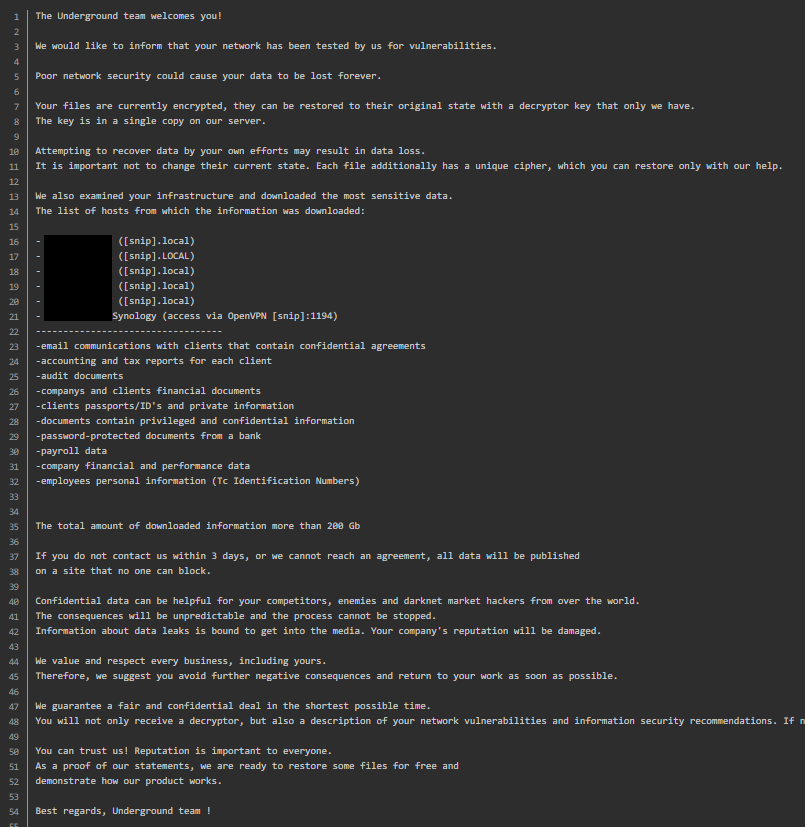

If you discover a message on your system, similar to the one above - you've likely been ransomed by Underground.
Underground (also referred to as Underground Team ransomware) is a relatively recent but increasingly active ransomware group first identified in July 2023. It has developed a reputation for targeting mid‑to‑large organisations across a range of industries — including manufacturing, IT, construction and professional services — in multiple regions such as North America, Europe, Asia and the Middle East.
Unlike many ransomware strains that change file extensions during encryption, Underground is known for a distinctive approach where encrypted files may retain their original names and extensions, making it harder for victims to immediately recognise the scope of the attack. It also systematically deletes shadow copies and system restore points, disables services like remote desktop access, and removes Windows event logs to hinder recovery and forensic efforts.
The group often gains access through spear‑phishing emails, malicious attachments, exploit of unpatched vulnerabilities, and credential theft, providing the foothold needed to spread laterally within the victim network. Once Inside, the ransomware combines strong cryptographic methods — such as AES and RSA — with additional operational tactics to efficiently encrypt high‑value data.
In line with modern ransomware extortion strategies, Underground leverages double extortion, exfiltrating sensitive data prior to encryption and threatening to publish it on its dark web leak site if ransom demands are not met. The ransom notes left behind often include detailed information about the compromised data and instructions to contact negotiation portals hosted over Tor and other anonymised networks.
Because of its evolving sophistication, broad geographic reach and the inconsistency in victim reporting, Underground is considered a serious and adaptable ransomware threat, capable of inflicting major operational and data loss on affected organisations.
Initial access is typically gained via stolen credentials or phishing, followed by lateral movement and encryption.
Underground ransomware first surfaced in July 2023, when the group began claiming initial victims and establishing its data leak presence online. After a brief period of lower activity, the operation re‑emerged in early 2024 with an updated leak site and renewed activity, signalling a sustained intent to target organisations globally.
Since its emergence, Underground has been connected to at least 26 publicly tracked victim disclosures, spanning sectors such as manufacturing, business services, and banking. Victims listed on the group’s leak site date from late 2023 through mid‑2024, suggesting consistent ransomware activity during that period.
Because not all incidents are publicly disclosed and some attacks may go unreported, the actual number of organisations affected by Underground is likely higher than the tracked count.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
“Just over one in ten businesses say they review the risks posed by their immediate suppliers.”

Solace Cyber was established in 2021, specialising in Cyber breaches, particularly Digital Forensics and Incident Response, Ransomware, Risk Management, and Information Security, along with Managed Security Services. The leadership team collectively possess over 20 years of experience in the IT and security industry. Solace Cyber is accredited to ISO 27001.
s
%+
A forensic analysis needs to be meticulous and a clean restore and recovery requires a wealth of experience not normally available in an in-house team who must provide a broader range of IT support skills:

Solace Cyber was established precisely for this scenario. We have a well-defined process for handling cyber-attacks like Underground, which involves a 6-step approach:
It includes a thorough digital forensic analysis from step 2 where the output becomes a central component of business recovery. This is because understanding the attack is of critical importance:
It is critical that the analysis of digital evidence is carried out to an agreed plan. This will have been designed to provide the best and earliest chance of discovering a root cause, which is essential to inform remediation/eradication and recovery as well as supporting a legal take-down case if this is applicable. A legal take-down means we can assist in the legal enforcement that stops the criminals from publishing the data, thus undermining the ransom notice.
Solace’s Digital Forensic and Incident Response teams maintain consistent communication throughout. Dedicated Incident Managers and technical engineering leads provide updates during the Cyber Incident Response journey, utilising risk registers and working within change management processes, all from triage through to post-incident, delivering successful business recovery.
Solace Cyber's assistance extends beyond the recovery phase. Following the restoration of your business operations, we collaborate with you to enhance your cyber security posture using a threat-informed methodology. This involves leveraging our Cyber 6 Step Process, designed to comprehensively address cyber threats and vulnerabilities.
Yes, Underground is a ransomware-based extortion operation.
A Underground ransomware attack generally enters a system in one of the following ways:
We recommend you adopt policies to:
After recovering from Underground, Solace Cyber recommends that you update your business continuity plan to account for lessons learnt during this attack & recovery.
The average cost of ransomware breaches hover around £500K, while smaller email data breaches typically incur expenses of around £50K. A critical decision emerges between preserving the environment for forensic analysis or opting for swift recovery to minimise business disruption. Delays in identifying and resolving breaches only exacerbate costs.
Cybersecurity insurance claims entail a multifaceted process, encompassing reasonable expenditures for investigation and remediation, alongside coverage for legal, business interruption, criminal liability, employment liability, and ransom policies. While the insurance industry plays a pivotal role in facilitating business recovery, cyber insurance is perceived as volatile within the sector, and many policies require meticulous validation.
Facing genuine pressure, there's a crucial decision to make - one that could rescue your organisation from weeks of operational standstill, reputation damage, and client data loss. Yet, the probability of a favourable outcome remains slim, emphasising the importance of engaging a specialised ransomware incident response team. They are your most viable recourse for navigating a ransomware incident.
The NCSC have documented the deliberations for paying ransomware: https://www.ncsc.gov.uk/ransomware/home
Important Reminder: It is a criminal offense to pay money to people who are subject to financial sanctions. The list of who is subject to financial sanctions is constantly changing.
The latest iteration can be found here: https://www.gov.uk/government/publications/financial-sanctions-consolidated-list-of-targets
Yes. There's a possibility that some of the lost data contains "Personal Data" belonging to your customers. Safeguarding such data is a legal requirement, so it's important to consider notifying the Information Commissioner's Office (ICO) about this incident, as well as your customers. https://ico.org.uk/
Your insurer or legal counsel will provide guidance on the necessary steps and how to proceed in this matter. However, Solace Cyber has experience collaborating with insurers and legal representatives and can offer assistance in managing these relationships during this challenging period.
Your business operations may experience significant disruptions. These could include:
To mitigate these effects, it's crucial to have a comprehensive incident response plan in place, including communication strategies, collaboration with cybersecurity experts, and measures to enhance system resilience and data protection. Additionally, transparency with stakeholders and proactive steps to rebuild trust can help minimize the long-term consequences on your business.
Action Fraud is the UK’s national reporting centre for fraud and cybercrime. Whether you have been scammed, defrauded, or experienced cybercrime in England, Wales, or Northern Ireland, Action Fraud offers a central point of contact for information on fraud and financially motivated cybercrime.
If your systems are showing signs of an Underground attack, REMAIN CALM.
YOU MUST NOT TOUCH THEM, RESTORE OR OVERWRITE THE DATA (explanation above).
Contact Solace Cyber on 01202 308818 or complete our form for a call back from one of our experts.
We will act promptly to reduce your business downtime.

Solace Cyber helps companies across the UK recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 14028838

Solace Cyber
Twin Sails House,
W Quay Rd,
Poole, BH15 1JF
United Kingdom